CANVAS Screenshots
CANVAS is updated frequently, so these screenshots may not reflect the current state of the product.
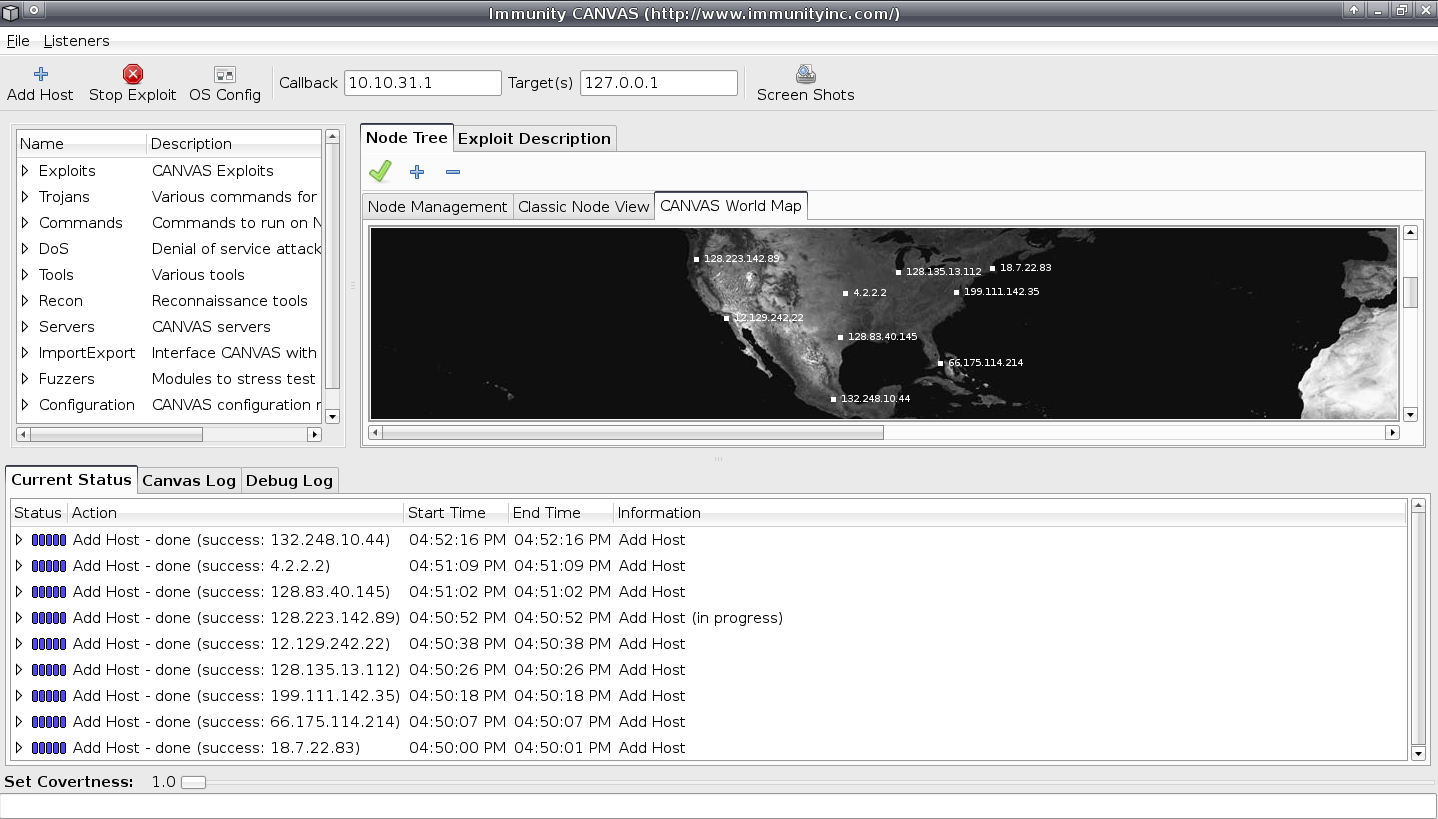 When enabled the CANVAS world map will reconcile IP addresses with their geographic location and
display that to the CANVAS user.
When enabled the CANVAS world map will reconcile IP addresses with their geographic location and
display that to the CANVAS user.
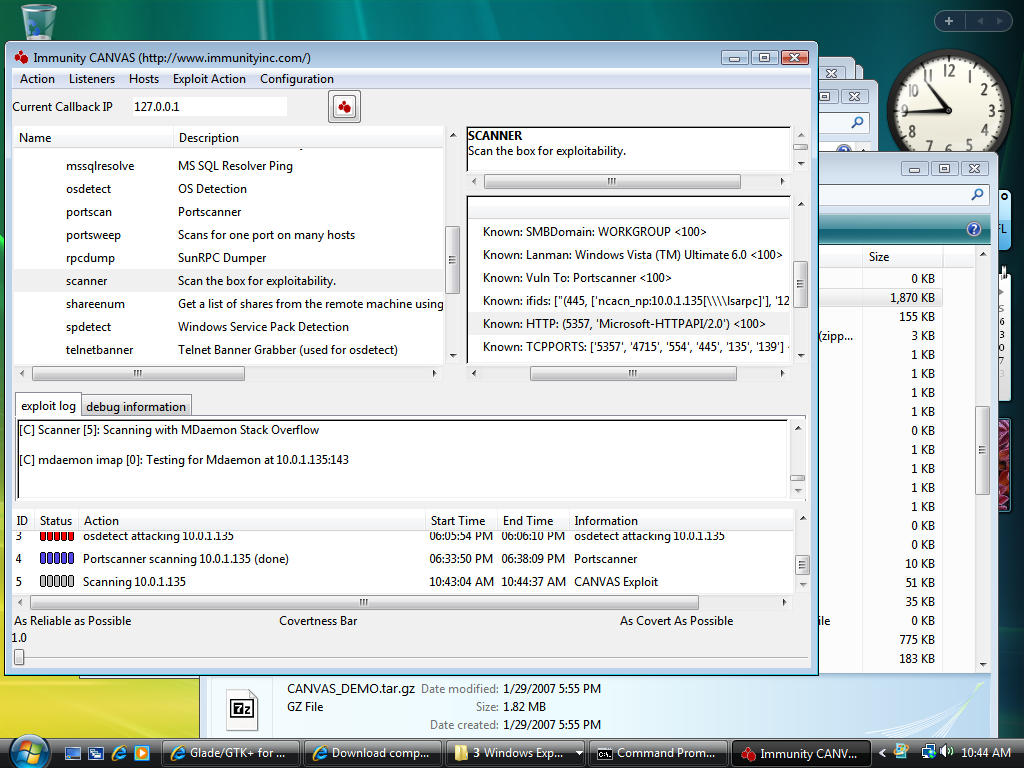
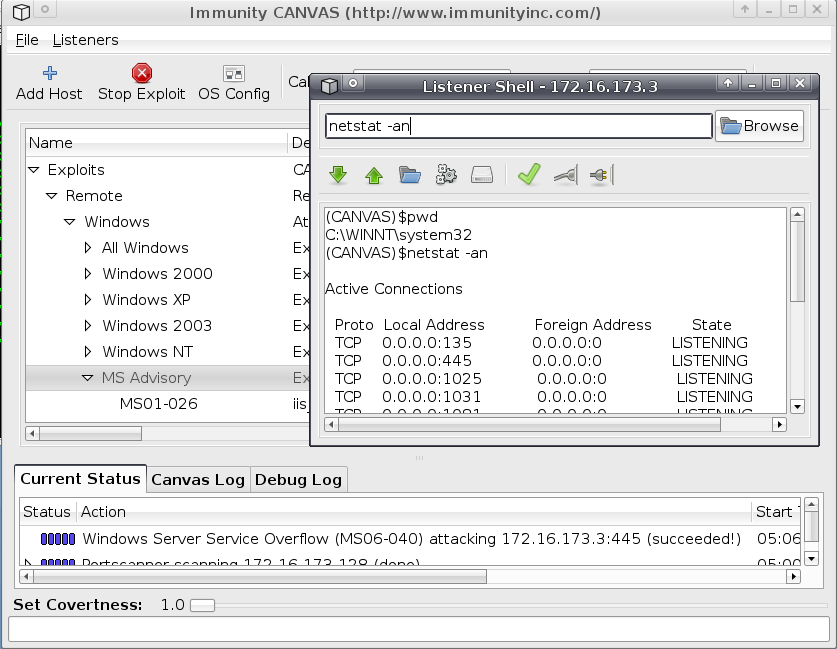 After successful exploitation of a host, the CANVAS user is presented with a listener shell which
they can use as a fully interactive shell or to launch post exploitation commands.
After successful exploitation of a host, the CANVAS user is presented with a listener shell which
they can use as a fully interactive shell or to launch post exploitation commands.
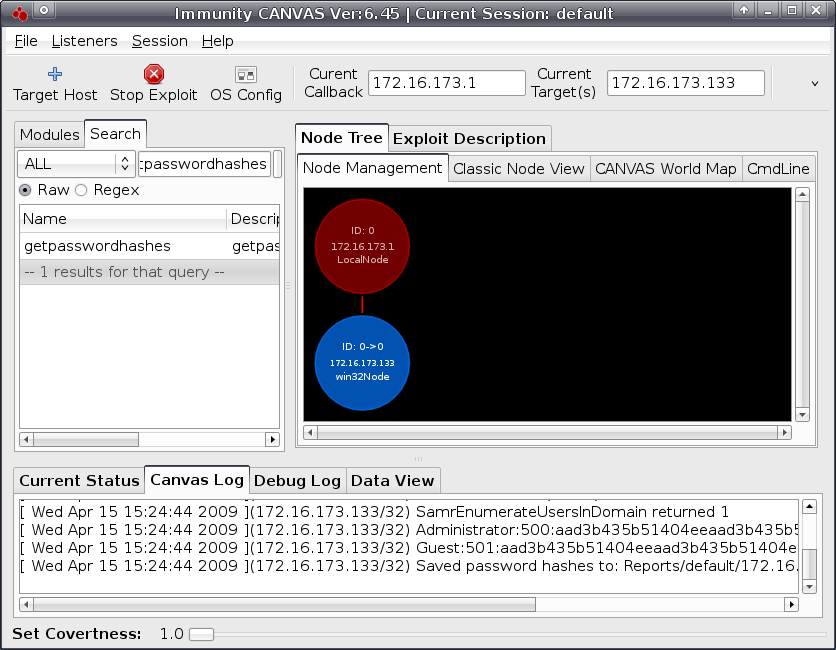 One of the many post exploitation modules available in CANVAS is the getpasswordhashes module
that will fetch hashes from the exploited host.
One of the many post exploitation modules available in CANVAS is the getpasswordhashes module
that will fetch hashes from the exploited host.
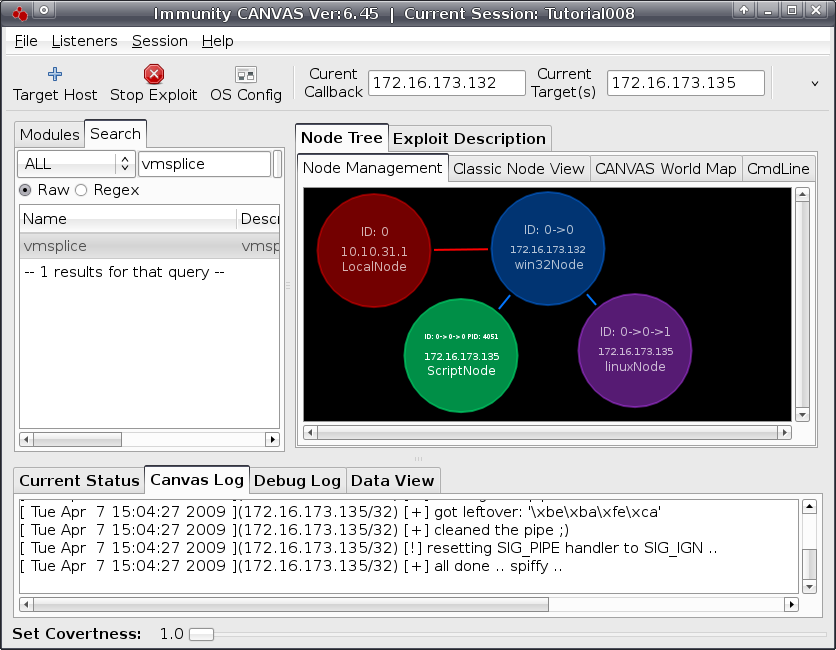 Using MOSDEF, CANVAS is able to use multiple hosts running different operating systems on
different architectures as pivot points to attack new targets. This is demonstrated here using the
Node Management node view which shows exploited hosts and their relation to each other.
Using MOSDEF, CANVAS is able to use multiple hosts running different operating systems on
different architectures as pivot points to attack new targets. This is demonstrated here using the
Node Management node view which shows exploited hosts and their relation to each other.
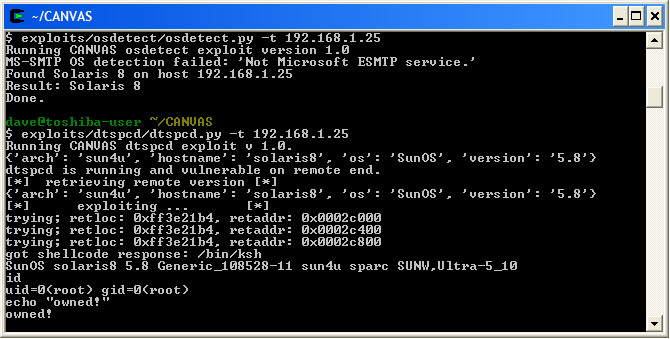 CANVAS can also be completely driven from the commandline, making incorporating modules into
scripts easy.
CANVAS relies heavily on the concept of a 'listener'. A CANVAS Listener is anything that needs to
respond to actions, such as a running exploit module, an open port waiting for a callback, or a
connection to a remote host that has been exploited. In this screenshot you can see one of the
advanced
CANVAS tools being used to print out all the available security tokens in the process that has been
exploited. Then the CANVAS user can switch security tokens to any of the found tokens, and attempt
to
access files as the new user.
CANVAS relies heavily on the concept of a 'listener'. A CANVAS Listener is anything that needs to
respond to actions, such as a running exploit module, an open port waiting for a callback, or a
connection to a remote host that has been exploited. In this screenshot you can see one of the
advanced
CANVAS tools being used to print out all the available security tokens in the process that has been
exploited. Then the CANVAS user can switch security tokens to any of the found tokens, and attempt
to
access files as the new user.
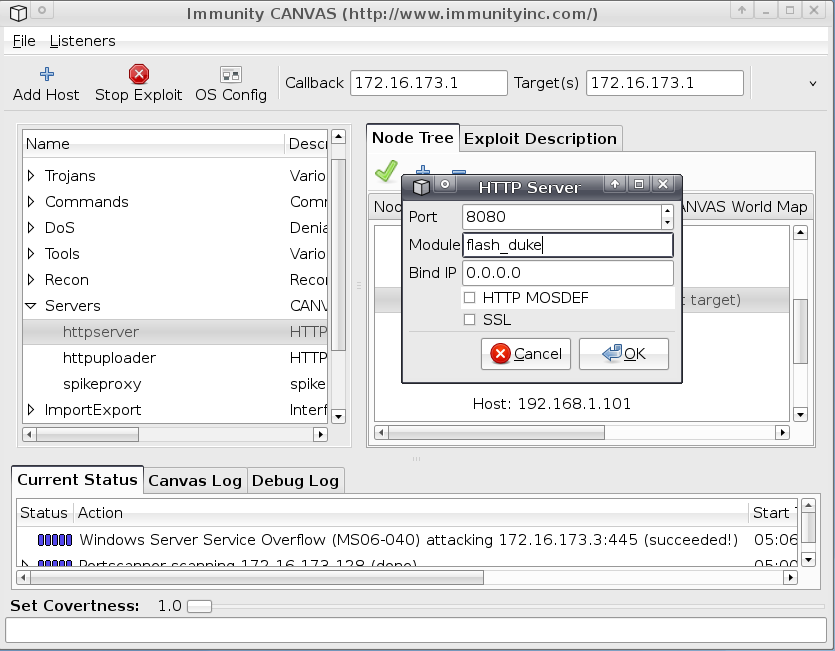
The Covertness Bar is a special feature of CANVAS that allows certain exploits to behave differently
depending on how covert the user needs it to be. For example, a high level of covertness can
sometimes
slip by application firewalls, since application fragmentation fools the firewall into ignoring the
traffic. Reliability and covertness are opposites on the Covertness Bar, as they are in real life.
CANVAS's multi-threaded architecture allows an advanced user to run multiple exploits at once, or
even
combine multiple machines' exploitation attempts into one console.
CANVAS can also be completely driven from the commandline, making incorporating modules into
scripts easy.
CANVAS relies heavily on the concept of a 'listener'. A CANVAS Listener is anything that needs to
respond to actions, such as a running exploit module, an open port waiting for a callback, or a
connection to a remote host that has been exploited. In this screenshot you can see one of the
advanced
CANVAS tools being used to print out all the available security tokens in the process that has been
exploited. Then the CANVAS user can switch security tokens to any of the found tokens, and attempt
to
access files as the new user.
CANVAS relies heavily on the concept of a 'listener'. A CANVAS Listener is anything that needs to
respond to actions, such as a running exploit module, an open port waiting for a callback, or a
connection to a remote host that has been exploited. In this screenshot you can see one of the
advanced
CANVAS tools being used to print out all the available security tokens in the process that has been
exploited. Then the CANVAS user can switch security tokens to any of the found tokens, and attempt
to
access files as the new user.
The Covertness Bar is a special feature of CANVAS that allows certain exploits to behave differently
depending on how covert the user needs it to be. For example, a high level of covertness can
sometimes
slip by application firewalls, since application fragmentation fools the firewall into ignoring the
traffic. Reliability and covertness are opposites on the Covertness Bar, as they are in real life.
CANVAS's multi-threaded architecture allows an advanced user to run multiple exploits at once, or
even
combine multiple machines' exploitation attempts into one console.
CANVAS VIDEOS
See CANVAS in action by watching the latest videos from Vimeo.
For product questions or purchase information
please contact us
866-524-4782 *
imu.sales@appgatedotcom
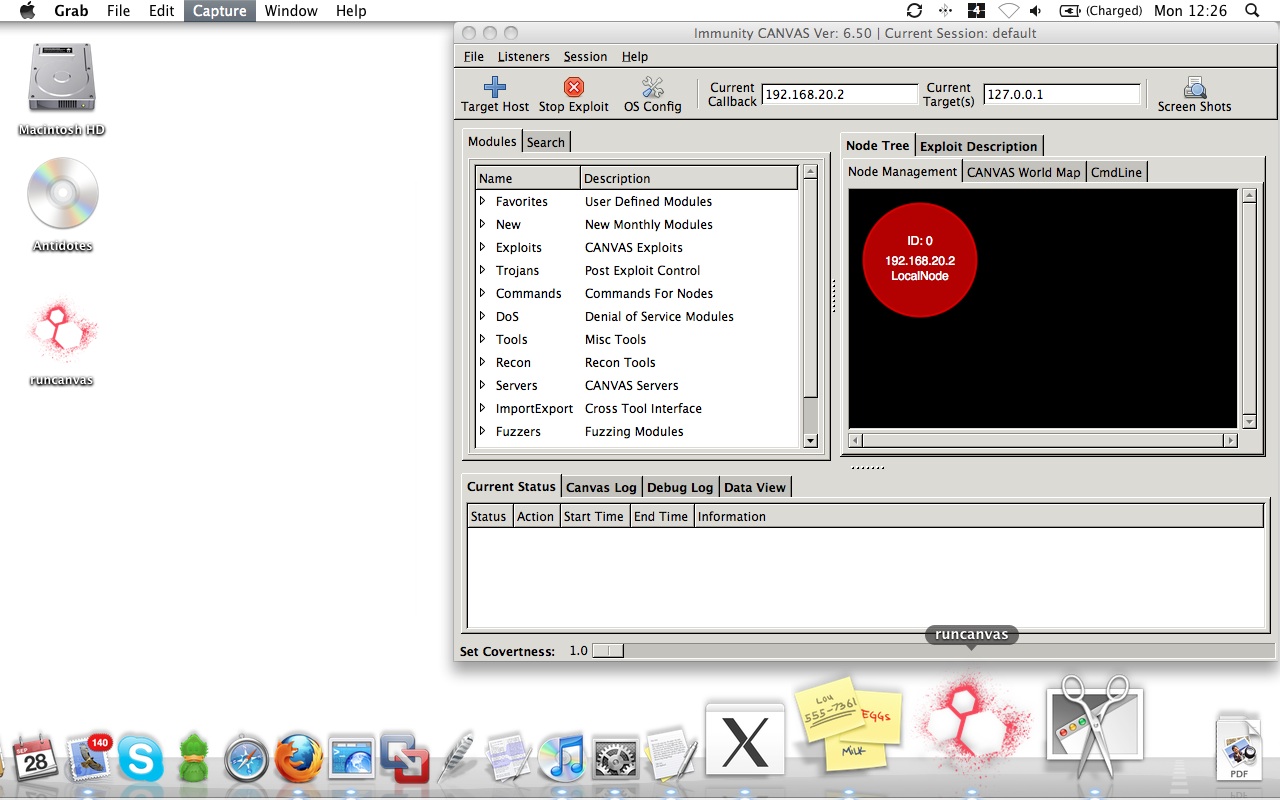
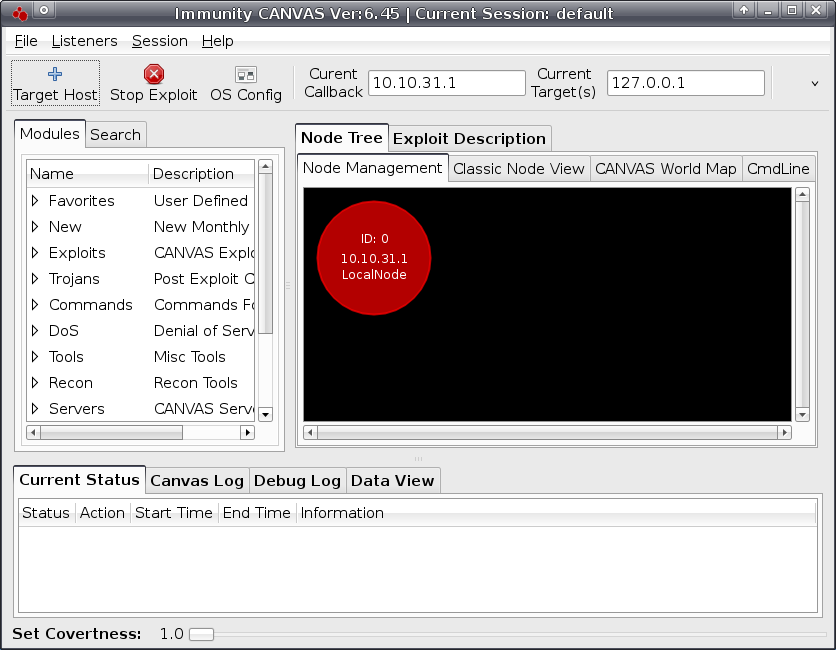 The default startup of Immunity CANVAS
The default startup of Immunity CANVAS